Let me preface this post by saying that I nitpick because I love. It seems that what started as a random nitpick will turn into a whole series of posts wot the “Cylons don’t use” in the title. This one is about encryption. Yes, I have another bone to pick with the writers. This time it is about this:
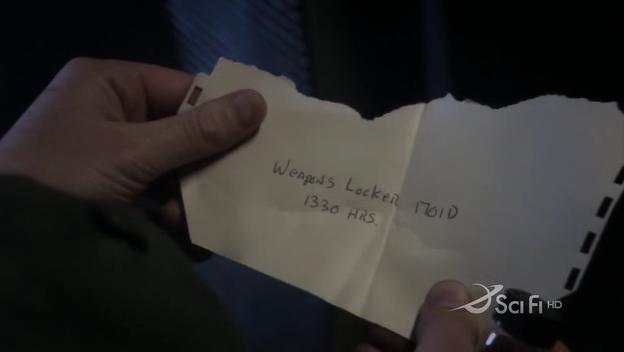
screencap © galacticabbs.com
This is the super-secret note that Colonel Tigh (a very senior military officer, and the former leader of the New Caprica resistance movement) passed to Chief Tyrol (who also had experience in NC resistance movement) about an incredibly secretive meeting which was accidentally intercepted by Tyrol’s wife Cally. This sort of thing happened to me too – back in grade school. Since then, I have learned to use encryption.
Let’s review – both Tigh and Tyrol are Cylons (if I just spoiled you, then go back and watch S3 finale already and stop complaining) and they must keep this secret. If anyone would find out about who or what they really are, their lives vrypotwould be in danger. Therefore keeping their true identity secret should be their paramount concern – and no effort should be spared to cover their own tracks. But here we have an experienced leader who had tons and tons of experience operating behind enemy lines make a colossal, bone headed mistake that might have exposed them. It is just stupid!
I do think about encryption all the time because of my education and my job – I’m conditioned to notice these things. A lot of people never even consider it. For example a housewife cheating on her husband may not have been exposed to concepts such as cryptography and information security so she may never even think about using anything but unsecured notes like this one. But these folks, for one have a military training. I have never been in the military so I might be wrong about this but I would think that security and simple cryptography would be part of basic training at least for officers. I’d think that they ought to know about cryptography in case they find themselves behind enemy lines, or in a position where all their communications are intercepted. If I’m wrong, please correct me.
Even if they didn’t get this knowledge in basic training, you can’t tell me they haven’t developed strong, low tech methods of encryption during the New Caprica occupation. Let’s face it – if a silly note like that ended up in the hands of the occupying forces it could mean many deaths, or loss of valuable resources. They simply could not afford to openly communicate their attack plans or resistance movement secrets in plaintext.
What should they have used? There are many low-fi methods to obfuscate or encrypt hand written notes. A simple Caesar Cipher would probably be good enough for plausible deniability in front of Cally. Would she be curious enough to try to crack it? Perhaps, but it is likely that Tyrol could easily play the gibberish note as some sort of an entry code he needed on a routine repair job or simply shrug and act as if it was just that – gibberish.
For real security they should probably use One Time Pad encryption. The pad is a long random sequence of symbols that is used as a key to encrypt and decrypt your message. This method was used successfully by CIA and KGB in the past. How does a pad look? It can be something like this:
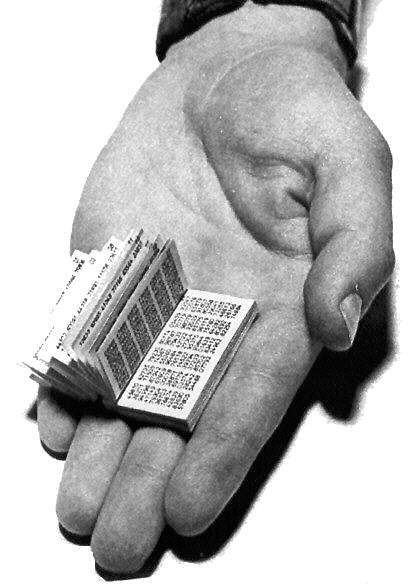
image © ranum.com
It is really a relatively secure method as long as you destroy the pads after each use, and you have a foolproof method of securely exchanging them. Our protagonists do have one, since they meet regularly. On each meeting they could exchange pads, which they would then use for written communication until the next meeting. The pads can be small and easy to conceal. A very nice disguise for a pad is a stack of papers with random stream of characters printed on one side, and unrelated hand written notes on the back. Plausible deniability – it’s just scrap paper – some gibberish spit out by some malfunctioning printer and you are just using it for personal notes.
When handled properly, it’s virtually unbreakable and in my honest opinion would be near prefect for this setup. But it seems that the BSG writers have never took a cryptology class. I’d say they ought to hire a consultant who could advise them on blunders like this one, but the difficult part is that an average person wouldn’t even think that this part of the screenplay would need to be looked at by a technologically clueful person.
So this is my BSG nitpick for today. I love that show, and this is why I hold it to a high standard and will ruthlessly pick on the little annoying little bits like this one. They simply destroy my enjoyment and prevent me from buying into the drama. I should be freaked out that Cally found the note and she will expose the final 5 but all I can think of is that C. Thigh is an idiot for leaving that note in plaintext.
Sigh… Sometimes I think I would enjoy TV and movies much more if I was just absolutely, technologically inept and clueless. :P
[tags]bsg, battlestar galactica, galactica, one time pad, caesar cipher, encryption, cryptography, weapons locker[/tags]
the OTP is *proven* unbreakable (the only one where it can be proven, see Schneier’s Advanced Cryptography book or any other student book on elementary crypto) if the chiffre is truly random and at least as long as the message you want to encrypt. there is no attack vector to reduce complexity even if the operation is a simple 1:1 XOR.
Yep, the problem is generating truly random data, and protecting it from getting captured or intercepted. This is why it is not really used in electronic encryption that much. For manual encryption though there are few better.
As a veteran of the US Army, I can confirm that security of transmissions is held to be of the utmost importance, and every recruit is trained accordingly. Security in general, and communications, specifically, is at the top of my list of things I know I will almost always have to suspend my disbelief about when watching shows with military aspects.
See people – there you go. :)
@Teague – if you don’t mind me asking, what kind of “low fi” encryption algorithm would military employ in a situation like the above? I man, if it’s not classified that is. :)
It’s a combination of syncronized frequency hopping by the radios, and a published book of “codes”. We were trained in effective use and quick disposal of both.
Of course, that should be synchronized….