Passwords are really bad from security standpoint. They positively, absolutely suck. You know how I know that? Because I can actually remember a lot of peoples passwords, that I never asked for. People just tell them to me while I help them with their computers. Or they write them on a sticky note and put it on the keyboard so I can log into their shit to fix it.
I don’t remember anyone’s birth dates, I can’t memorize my own phone number but I can recall bunch of stupid passwords (that I don’t care about) from the top of my head. Why do they get stuck in my memory? Because they are way to simple. The super-secret password of some random guy on the street is usually the name of their wife, girlfriend, mistress, son or pet hamster followed by the year and/or purchase of birth of said creature. Or their favorite sports team – you know, the one they always talk about.
The most common passwords out there are not love, sex, secret and god or whatever else The Plague (that poseur) came up with in that one movie. No, the most common passwords are jenny57, john81, riders66, hunter2 and of course password123. Short, sweet, easy to guess, easy to remember, vulnerable to a dictionary attack, helpless against rainbow tables.
That’s just how it is.
Why? Because people don’t give a fuck. Identity theft is some shit that happens to “other people” and not you, so why would you even bother? No one outside our industry cares about passwords or security of their online accounts. No one!
Sometimes I wonder if “normal” people think me a creep, seeing how I am super secretive about my passwords and accounts. I have passwords on everything, I always lock my machine when I leave my desk. My behavior is probably setting off red flags everywhere. Being security conscious is just not a “normal” thing.
A “normal” thing is this:
“My password is hunter2 – I use that for everything including my bank, har, har, har. Don’t tell anyone!”
I always balk when they do that. Why would you tell that shit to anyone? Why would you jeopardize every online account you own? Why would you risk some dude getting their hands on all your hard earned money. You can tell that stuff to your wife, but not to some guy you work with, or are distantly related to. I know I’m a handsome, trustworthy and honest looking guy. Ladies tell me this all the time (usually right before they announce they prefer to be “just friends” cause I’m cool like that). But that is no reason to trust me with that vital information.
I also like this gem:
“But what could anyone do with my Gmail password? Read my spam? Hardy, hur, har, ha! Am I right?”
Yep, totally right. They wouldn’t be able to do nothing. They surely wouldn’t abuse the “I’m dumb and I forgot my password again” feature of every website in existence to issue password reset requests, that would collect in your inbox and give them access to everything you have ever signed up for. Nope, that would never happen.
And it’s not like you use that very same username and password to log into your bank, isn’t it? It’s not like your bank sends you emails with your bank account number and other useful info to that Gmail address, so that the bad guy would instantly know where to go to steal your money. No, that would be silly.
After all, you are not rich, important or interesting enough to warrant such attention. Identity theft only happens to those other people, but not you.
Ignorance, denial and stupidity do not change the fact that passwords are, and have always been a really stupid idea. No one in their right mind will actually come up with a long secure password that would not be vulnerable to a rainbow table attack because they are not going to remember them. It’s just not possible or practical. If you will force them to create such a password, they will write it on a sticky note and glue it to their monitor so they don’t have to look for it 17 times a day. If they don’t care about the security of their own personal email account that everything else they have ties into, they surely won’t care about the account on your service.
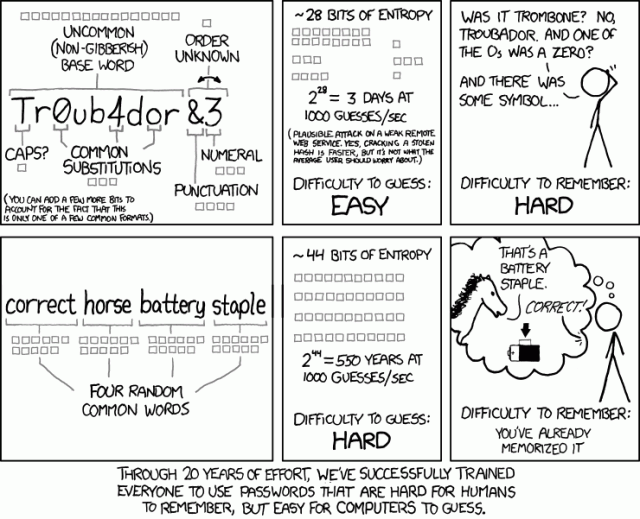
Of course there are things that are more secure than pass-WORDS. Pass-PHRASES for example are infinitely better, easier to remember, more robust and less vulnerable to all known attacks. But that boat has sailed a long time ago when everyone on the internet collectively decided that pass phrases can go fuck themselves in a corner while wearing a bowler hat.
No one uses pass phrases. Let me rephrase that, there is no service out there, that I know of, that encourages it’s users to use a pass-PHRASE instead of pass-WORD. Those services that even bother to force their users to employ more secure passwords, usually do it by telling people how many upper and lower case letters they should have, how many numbers, and etc. So what do people do?
They use JeNnY57, JoHn85, HunTer2 or if you are really strict passWord1@#. Still easy to guess, still vulnerable to a dictionary attack capable of capitalizing letters, and still included in every single rainbow table ever made. And of course users get pissed, because they can’t remember the exact capitalization they used so they end up gluing this one to their monitor as well. Wouldn’t it be more secure if they could use something like this instead:
My friend HamsterFace doesn’t wear his parachute pants on Tuesdays.
How much better is that than HunTer2? It’s way much better, that’s how. Let me count the ways:
- It’s goddamn long
- It has capitalization
- It has non-alphanumerics
- It doesn’t have any numbers, but look how fucking long and complex that is anyway
- It ought to be easy to remember unless HamsterFace will start wearing his stupid pants on Tuesdays
Now, tell me who will let you use an awesome pass phrase like that in their service?
No fucking one. That’s who. Be honest, that pass phrase wouldn’t work in your own service wouldn’t it? Cause you probably used VARCHAR(32) for the password field didn’t you? Cause, you know – we might run out of fucking bytes or something when we get seven billion users and become the new Facebook or something, right? No? You VARCHAR(64) then? Tough, it still won’t fit, cause that baby is 67 characters long.
Wait, stop. Rewind. Why are you not hashing and salting that entire thing? Why does it even matter how long the password is? It still will hash to a fixed byte value no? So why would you even care what the user types in?
Did you, per chance, decide to make the password character array variable with a fixed to save memory instead of using a string like a reasonable and non-stupdid person would? You know, in case your theoretical seven billion users all try to log in at the same time? Or is there some other contrived reason why you wouldn’t handle longer passwords? Was your hash function taking too long perhaps, so you decided to optimize it instead of not giving a fuck? I mean, users only log in every once in a while – if it takes a few seconds longer than usual page reload, that’s perfectly fine. No one cares, as long as everything else is fast. But you optimized it anyway, didn’t you?
You know what? I won’t deny it – I did it too. Not recently, not all of this, but I have created really, really, really stupid log-in schemes in the past. I’m just as guilty as the rest of the internet. We are all stupid like that. Premature optimization is like premature ejaculation – you don’t think it will happen to you, but then it feels good in the moment, and it just does. Afterwards you get terribly embarrassed, and you don’t want to talk about it when someone calls you out on it.
It happens to everyone – especially when you are young and inexperienced. I’m of course talking about premature optimization, not that other thing – that never happened to me… And never will cause I’m awesome at “the sex”. Like level 85 in it so fuck you. The point is we shouldn’t optimize to early.
Ideally password fields ought to be unbound, and allow as much crap as the user is willing to type in. If they want to paste the entire text of The Great Gatsby in there, let them. Why not? Giving your password a reasonable character minimum on the password field responsible and praiseworthy. Putting an upper character limit on it is… Beyond stupid. Let me use an analogy to explain to you just how stupid it is. Otherwise you might not get it, and I will have to explain again and we don’t want that.
If you are an American, and you went to high school sometime this century you probably had a locker with a cheap combination padlock. You also probably had that friend who would “prime” his padlock with the correct combination, so that he wouldn’t have to enter it upon returning. He would go to class, smoke a cigarette in the bathroom, then prance over to his locker, pull on the lock and it would just open. He could have not bothered with the whole padlock thing at all, and just leave the damn thing unlocked – but you know, stupid is as stupid does.
And then that one time some asshole stole all the shit from his locker, and he was outraged and baffled how this could have happened. A genuine genius, that friend of yours. I bet you can’t wait to see him at the reunion.
If you are not an American, go watch any High School related movie and/or TV show that was made in the US and you will see what I mean. Those lockers in the hallways – you put your books and your jacket an your illegal drugs in there when you go to class and write BASIC programs on your Texas Instruments calculator while the teacher drones about some shit you actually know more about than him. That’s what everyone does in High School, right?
The friend is the guy who always walks up to the main character while he is putting shit into the locker, and talks about really stupid stuff. The one with the dumb face. You can’t miss him – he is in every movie.
Are we all on the same page now?
Yes?
Good. Let’s continue.
When you put an upper character limit on your password field, you are actively encouraging your users to be that friend. And if you have other arbitrary restrictions then you are even worse than that.
Guess ho has the stupidest arbitrary character restriction on their passwords? Just make a wild guess?
Give up?
Banks.
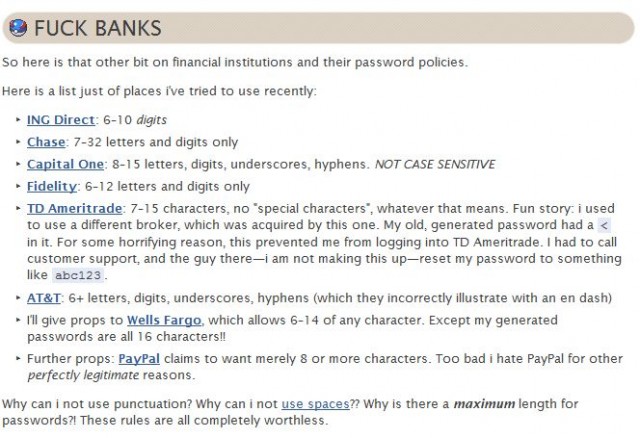
Yep, the people who you trust with your money have the dumbest rules about what characters (and how many) you can use in a passwords that will protect your life savings from evil dudes from the internet. There was this great article out there aptly titled FUCK PASSWORDS where I found this here gem:
Go read the entire thing – it’s funny, insightful and also humorous. As you can see, the author makes a clear case here: banks are pretty much the worst offenders when it comes to mind bogglingly stupid, arbitrary password restrictions. They should be the guys that insist that you use the strongest and most annoying passwords, but instead they force you to use short, and dumb ones.
Why? I don’t know. Perhaps their programmers suffer from that premature ejaculation optimization problem we talked about. Perhaps their back end is a legacy FORTRAN or COBOL system, and passwords longer than 10 characters just don’t fit on the punch cards. Perhaps their entire online thing was written by the 13 year old nephew of the CEO. Who the hell knows. There should not be any reason for these restrictions, and yet, here we are.
Compare this to Twitter which just cares that your password is longer than six characters. Any characters – mind you. Not just the nice ones. Not just plain ASCII with no spaces or symbols. Any fucking thing you want.
Compare it to Google or Blizzard who will let you use two factor authentication. You know what that means? That means that even if a bad guy guesses that your password is “hunter2” (you know, cause you told him at least twice) he still won’t be able to get in. He would also have to steal your phone / key fob, and guess your password at the same time. Which is way harder than breaking into your Chase account. They could break into your bank while sitting on their couch, eating Cheetos and calling people “fags” on Xbox live. To hack into your Gmail or WoW account they would actually have to:
- Get the fuck up
- Turn off Xbox
- Put pants on
- Wipe Cheetos stained paws on said pants
- Leave mom’s basement
- Locate your ass in this here physical realm
- Steal a physical thing from your fucking pocket without you knowing
- Then guess the password
Most of these guys don’t actually go through with any plan that requires them to do anything beyond step 5. I mean, if you actually have to go and interact with the dude you are trying to rob face to face, this thing becomes serious business. You might as well stay home and break into his bank instead.
I know this whole password bullshit seems like like something that was made up by Terry Pratchett or Douglass Adams for the sole purpose of being satirical and silly. Sadly it is not. It is real life. In fact, these two guys are not nearly as funny as you think they are – they are just good observers of how really, really stupid we behave as a species.
I swear, sometimes I feel like the few of us here, on the internet are the only fucking sane and coherent people left in this world. Everyone else is either to stupid to be a productive member of society, or just completely of their rocker. Then I remember it’s just the observer’s bias, and that we are just as bad as the rest of them. We just excel at being stupid in slightly different ways than they do.
And yet the world keeps on turning.
Great rant today, Luke. Extra piquant.
Recently I have started to forgot passwords… Nothing is so annoying than resetting the same password twice in the same day…
I try to keep my passwords secure and unique, but I just can’t remember all of them…
Then something like EA leaks passwords, time to change 5+ gaming site passwords…
Openid is one way, but it’s hard to implement/explain to regular users.
My online banking has a maximum of 5 characters
true story!
A couple of points after this excellent post:
* I used to have a pass phrase for my MSN account. That was until these fuckers decided to force me to change it every month. What was wrong with my perfectly good pass phrase? I don’t have MSN any more, so I don’t care, yet it still annoys me.
* My bank uses no password at all. To access my online banking, I need my bank account, my pass security number (both available on my bank card) and a made in China, US patented Vasco electronic box wich churns semi random number pairs that have to match whatever is generated on the server. Sounds fool proof really, until my sister pointed out to me that the cycle of “random” number was no random at all and repeated every 12 transactions or so…
* I particularly like your last point. I was feeling slightly aggravated by your post, considering that I am guilty myself of using way too easy passwords (similar to the Troubador example you gave). Then I read the ending and I paused to consider how angry I often feel at how journalists, politicians or any member of the public often speak about topics where I know my stuff. Like, say, European institutions or international shipping. 99% of what you read or hear about this in the media, politics or the general public is completely useless, utter crap, completely and absolutely wrong. And yet, Europe exists, international trade continues, the world keeps turning.
@ k00pa:
The problem with OpenID is that everyone wants to be a provider, but no one wants to be a consumer. Plus I heard horror stories about glitches on the provider site, locking people out of their accounts, and the black-flips consumers had to go through to get it fixed. It is problematic to say the least.
As for user education, I think the secret is not to call it OpenID. Just put a button that says “Sign in with Twitter/Facebook” up there, and people won’t have any problems getting in, and they will happily go through the authorization click-through. Clout and Disquss do it that way and most people don’t have any issues using them.
You mention something about OpenID and people will instantly panic and soil themselves out of fear.
@ MrJones:
@ Alphast:
Holly crap… It’s almost harder to make a cyclical widget like that than a pseudo-random one. I thought you were going to mention it is not truly random because you can guess the seed or something, but this is just ridiculous.
@ MrJones:
Seriously? Care to share what bank it is? So we can all “test it out”, for noble reasons of course.
My fucking home router has a maximum of 14 characters for password and IT DOESN’T SAY IT ANYWHERE in the interface. And it let me type in 16-character password and save it, but then it didn’t let me in. First time I didn’t get what happened and restored factory settings. Then, naturally I tried again with the same password, with the same results. Then I just guessed about 14 characters, removed two and successfully logged in. Fuck those developers very much, excuse my Klatchian :)
At the office we have a crappy piece of sowftware, ‘home brewed’, and aptly named SSExplorer. Because that pile of dung was written vey long time ago in Delphi or something, it uses 8-character user names. Due to this limitation people with longer last names often get rather funny usernames, but it is also very hard to guess person’s real name from that chopped thing. Why would you need that? Because that 8-character atrocity is also your corporate email address. So by looking at the corp. email address it is next to impossible to guess who that person is. But I digress, we were talking about passwords. Well, for that software you get a note in the envelope with your password (random letters in random case) and YOU CAN’T change that thing. Not EVER. I have it in txt file on my desktop because I refuse to remember it.
Oh, and why do we use that software at all… it has ALL the info on employees, from salary to promotions to vacations to sick days. For all eternity :) Ah, and what it is that we do as business… create software :) websites, mobile apps, even desktop apps :)
Hmm. I read somewhere that a lot of banks force wierd arbitrary limits on user passwords to prevent users from reusing passwords they have everywhere. Because reusing passwords is a much bigger problem than easy to guess ones (login delays and proper hashing solves the latter problem in a big way,) forcing a user to come up with a special password just for this site is big boon for security. Sure, it annoys those of us who know how to use passwords, and already have a good system, but for the unwashed masses… probably saves the banks a lot of headaches.
At least that’s what I read. It could be hogwash.
Well, I’m “outside your industry” and yet I’m the weirdo who usually “annoys” friends and family by making the same complaints. I ranted about it to one of the customer service folks after setting up my credit union account, too, and they just shrugged and repeated the “it’s for your security” mantra while I tried to point out how restricting characters and lengths of passwords made security worse. *sigh* Seriously, this is 2011 – yesterday’s future FFS – and you can’t at least support 20 char’s of ASCII?
Oh, where to begin…
1. My Bank, Westpac, insists upon a six character password containing letters and numbers. It cannot be shorter and it cannot be longer. As an aside, you can’t type it in manually, you have to click the buttons on the screen with your mouse to stop keyloggers unless you’re on your phone.
2. My savings bank, RaboDirect, only require that I know my client number and then I have to punch my code into my Digipass doover thing which spits out a six digit code to punch in as a password.
3. Macromatix, a backoffice system that one of my places of employment use, has case insensitive passwords. Considering that if someone got in as a manager they could see a lot of details about the store that they run (and I mean a lot of stuff, financials, employee details, all sorts of stuff), it’s probably not a good thing. Not sure about password lengths but it likes my eleven character long password with assorted things in it.
4. The training system used by the same place of employment is over the top crazy: it requires that you use a password at least eight characters long with at least one upper case letter, one lower case letter, one number and one symbol. The average employee will use it once a year after they finish their initial training to take the “What To Do When The Store Is On Fire And Other Assorted Common Sense Things That You Should Already Know” test.
5. My other bank, Commonwealth Bank, requires a password that’s at least 8 characters long but not longer than 16, must contain letters and numbers, can’t be the same as my last five, shouldn’t contain a part of my name or DOB, can not contain my client number, and can contain pretty much anything except these: ^`{}~=
6. Another place of employment has a backoffice system that uses the same logon details as the POS system, which is a four digit username and a four digit “password”. But this one is only (AFAIK) accessible internally so it doesn’t make much of a difference anyhow.
My bank requires two-factor authentication for privileged access (i.e. doing stuff other than checking my balance and transferring funds between my own accounts). I used to think this was pretty common with online banks, but I guess I’m just lucky.
@ Luke Maciak:
But what if I don’t have Twitter and I don’t want to use Facebook? I have seen sites that have only those, and won’t have custom OpenId providers supported.
Kim Johnsson wrote:
That is the only thing that keeps my hair from turning insta-grey.
The password-system of my bank is so laughable simple.
5 characters. Not more nor less. And no signs except the ones you’re allowed to use in the transaction form…
Result? Most people seem to use their credit card ID with one added letter or number :/
I try all of my passwords as a randomized string of 100 characters. Most rule out spaces, many rule out “special” and brackets, and I have never seen one that would accept all 100. My router takes 63 with no restriction on what characters I use. I don’t know what Google does as I self limited it to 20 so I could remember it on PATs, and I use the authenticator and application specific passwords for anything that signs in to my account. I switched from WF to a local bank and my password more than doubled in length and let me use a whole lot more character types. The only problem I have with them is they require numbers in your login name.
Also, why my browser on mac is Netscape O_o I think I used the iPod browser inside the Twitter app.
The only logical option is to change this scenario, aggressively. We will ridicule every programmer/website developer/whoever who caps the password length to anything less than 500 characters or so.
Also, might I add, I was mildly shocked to find out that bank websites out there use… persistent passwords? Over here in Finland a few banks (probably all of them) hand out a list of passwords to each customer, and while the passwords are short, they are all disposable, one-time, and you have to use them in the same order as they appear on the list. So as the customer you have to punch in your login ID and then the one-time password. Should you lose the list, you might be fucked, but the thief would still have to know the login ID which is always numbers-only, and never printed on the list.
@ Liudvikas:
for noble reasonsfor science.FTFY
@ Victoria:
Our company uses first initial + last name which has been working out fine so far. All the emails have been unique so far and quite easy to guess/recognize. We also had some funny ones. One guy who worked for us for a few week was W. Hoops so his email became whoops@companyname.com. He got fired fairly quickly and the management decided that he was a whoops indeed.
My university uses last name + first initial so I’m always logging into the wrong systems with the wrong username. :)
@ astine:
That is very likely their “official” cover story for 6 character password length limit. I still like my punch card theory the best.
@ StDoodle:
Well, seeing how you read this here blog I consider you a honorary member of the industry – even if in spirit only. I’d print out and send you a certificate of achievement or something but I’m lazy. :)
@ Douglas:
Six characters exactly? Wow… That’s… I have no words.
Actually, I do – I wonder how many people chose their six characters to be “FUCKOF”.
@ Kim Johnsson:
You are lucky.
@ k00pa:
Then you put a small link next to FB, Twitter and Google buttons that says “Other”, and gives you access to full set of OpenID options. Those with custom OpenID ought to be smart enough to click on it, while the dummies will be distracted by the big colorful ones long enough to get scared of it. :)
@ Morghan:
This is actually pretty clever. Use a really long and difficult string, and let the service itself pick a subset of it. I like this!
@ k00pa:
The browser detection plugin I use has sort of became abandoned by its creator. It has not been updated in years. One of these days I will sit down and make sure it properly detects mobile browsers…
@ axebeer:
Wow, nice. One time pad approach to bank security. This is actually pretty neat.
Ok, I was only able to skim before my last post, so now that I’ve read further, here are my additional thoughts:
1) People don’t care because anything on a computer isn’t “real.” Don’t give me the rational argument against this; it’s an emotional response, not a rational one. I work in the construction industry, technically, and I can’t tell you how many times people insist on getting a fax because it’s more “real.” Of course, lack of internet access in this country doesn’t help either (yeah, when the building’s done it won’t be an issue, but try getting a good connection on a job site without getting raped by your cell phone provider if you use it constantly; but I digress). On the low end, people tend to think of everything in those mysterious boxes as “magic,” while on the mid-range it’s just an appliance. On those of us geeky about these things in general see it for what it is enough to worry about such things.
2) One really good & complex pass phrase (you can combine a full pass phrase with various symbolic substitutions for a decent “password”) + KeePass + syncing (I use SpiderOak personally, but whatever; just be a bit more careful if you use dropbox) and you’re set. My wife has an “in case of emergency” envelope with my KeePass passphrase/word, and it has everything else. There’s a copy on my laptop, my work computer, and my phone; if all three are lost, the town was probably nuked and my passwords are the least of her worries. ;) Actually, one could also re-download KeePass and grab the database from SpiderOak; don’t worry, I store the password in KeePass, so it should be…. oh damnit.
@ Liudvikas:
http://www.postbank.de
@ MrJones:
Oh no! It’s in German! My evil plans are ruined by the language barrier! :D
Luke,
I think when our loved ones are affected it affects us the most.
Not to mention the entire industry built off of identity protection.
I think StDoodle had a good point:
I try to continue to help my loved ones do better with their passwords. What’s interesting is a lot of people are used to using one handle online as well.
Compare that to possibly tracking a user down on torrent sites via their information already given.
I think xkcd made a good point, and it’s a shame we have conditioned ourselves to think that way.
What annoys me more is having restrictions on what your password must or must not have. Let the user know that they are being an idiot by selecting such a weak password and then move on… I don’t believe it’s their place to dictate what I use as my password, and frequently it requires me to use a password that I forget frequently and thus would have to keep in an excel spreadsheet or something else… which makes it less secure.
I used to use: travi$l0ve as my “go to” password for various services but I finally had to abandon it because some services didn’t like the $ and others said I would have to have a capitol letter, etc etc. (to anyone reading, this password has been totally phased out except maybe one or two throw away services I do not plan on ever using again).
While I recognize the above isn’t the worlds STRONGEST password, for the time being I am not Julian Assange and I just want a password that is going to keep most people out, and if someone want’s access to my accounts bad enough they will get in regardless.
What IS dumb is Fatcow’s rule for email addresses that they must be between 6 and 8 charaters long and can only be alphanumeric. My email passwords are always my strongest passwords (because they are my fucking email passwords), so I don’t use their email platform.
Worst I have come across is http://www.virginmobile.com.au, your user name has to be your phone number, and your password has to be nothing but exactly 6 numbers.
lawl @ story about guy in the basement