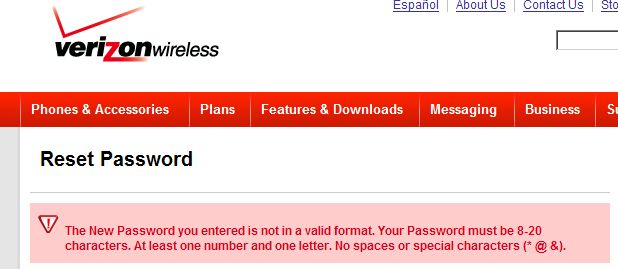
I was changing my password for my Verizon Wireless account and I suddenly saw this message:
If you can’t read that, it essentially says that passwords must:
- be 8-20 characters long (somewhat good practice – more characters the better)
- contain at least one letter and one number (very good practice)
- have no spaces or special characters like @#$%^() and etc.. (retarded to the max)
In other words, Verizon tries to force people to make secure passwords by taking out the two strongest types of passwords: complex passwords, and pass-phrases. Why are these passwords so strong? Because they are hard to crack using rainbow tables (yeah, fuck the dictionary attack).
Let me demonstrate – to crack the verizon passwords I only need roughly a 3GB rainbow table table for alphanumerics and numbers. I’m guessing the size by looking at the available downloads from Project Rainbowcrack. What would happen if Verizon allowed special characters and spaces? Well, then I need the 64GB table, lot’s more time and much more RAM to boot.
So while I appreciate their effort to force users to mix up letters and numbers, and to get away from using very weak 4-5 character passwords, they still fail miserably at security. If you are implementing any password security at all why not implement the correct one – allow spaces, and encourage users to create 3-4 word passphrases that contain special characters, letters and numbers. Hell, I’d allow full range of accented unicode characters so people could use a password like: Śął@#$ Ó&*ż ćęŁ. And yes, I just made it up – I don’t use this string for a password.
Sigh… Half assed attempts at security like that annoy me. In fact, implementing such security may actually decrease the average strength of the passwords among your users. Some power-users probably will always utilize a strong passphrase if they are allowed, and some people will always use dumb passwords vulnerable to dictionary attacks. Verizon’s policy means that the passphrase users will have to use something less secure, while the security blind retards will just tack on their year of birth onto their regular password (ie their last name) and call it a day. And as you can imagine, this won’t make their password any less vulnerable to dictionary attack. So your cutting out large number of very strong and secure password schemes, without really forcing the worst offenders to use anything stronger.
[tags]verizon, verizon wireless, password, password security, password reset, rainbow tables[/tags]
Pingback: Terminally Incoherent » Blog Archive » Strange Password Restrictions
